Network Configuration: Difference between revisions
No edit summary |
m (→Setting up FileZilla Client: 123.123.123.123 on port 24*256+55 = 6199) |
||
| (351 intermediate revisions by more than 100 users not shown) | |||
| Line 1: | Line 1: | ||
Setting up network components for FTP is not trivial for use outside your LAN (Local Area Network). Since so many firewalls and routers exist, it is impractical to give detailed step-by-step instructions suitable for every user. It is important to understand the basics of the FTP protocol in order to configure FileZilla and the routers and/or firewalls involved. | |||
This documentation describes the history of the FTP and how some aspects of the protocol work. Reading it carefully will save you a lot of trouble setting up FTP. | |||
== Background == | |||
This section provides an overview of the historical and technical background of the FTP protocol. For detailed in-depth information see [[File Transfer Protocol|specifications]]. | |||
=== | === Historical Background === | ||
In the fast living world of the internet, the File Transfer Protocol is not just old, it's ancient. Early drafts of the protocol go back as far as 1971, and the current specifications are from 1985. The protocol might even be older than you! | |||
Back then, the Internet was mainly used by universities and research centers. The community was small, many users knew each other and all were collaborating together. The internet was a friendly, trusting place. Security was not much of a concern. | |||
A lot has changed since then. The Internet is now ubiquitous, with millions of users communicating with each other in many different ways. | |||
It is also a more hostile place. The availability and openness has attracted malicious users who exploit design limitations, incomplete implementations, bugs, and the inexperience of other users. | |||
Several attempts have been made to address these problems: | |||
* [ http://en.wikipedia.org/wiki/Network_address_translation NAT ] ( Network Address Translation) | * [http://en.wikipedia.org/wiki/Network_address_translation NAT] (Network Address Translation) routers. Many hosts and routers on the internet use the [http://en.wikipedia.org/wiki/IPv4 IPv4] protocol. The number of hosts connected to the internet has reached IPV4's design limit for the number of addresses ([http://en.wikipedia.org/wiki/IPv6 IPv6] is designed to relieve this). NAT routers allow multiple systems within a LAN to connect to the outside world with one external IP address. | ||
* [ http://en.wikipedia.org/wiki/Personal_firewall | * [http://en.wikipedia.org/wiki/Personal_firewall Personal firewalls] try to protect personal computers from attacks by malicious users. | ||
Unfortunately, both NAT and personal firewalls conflict with FTP more often than not. To make things worse, some are themselves flawed, causing additional problems regarding FTP. | |||
=== === | === Technical background === | ||
What distinguishes FTP from most other protocols is the use of secondary connections for file transfers. When you connect to an FTP server, you are actually making two connections. First, the so-called ''control connection'' is established, over which FTP commands and their replies are transferred. Then, in order to transfer a file or a directory listing, the client sends a particular command over the control connection to establish the ''data connection''. | |||
The data connection can be established two different ways, using ''active mode'' or ''passive mode''. | |||
In passive mode, which is recommended (see below), the client sends the PASV command to the server, and the server responds with an address. The client then issues a command to transfer a file or to get a directory listing, and establishes a secondary connection to the address returned by the server. | |||
In active mode, the client opens a socket on the local machine and tells its address to the server using the PORT command. Once the client issues a command to transfer a file or listing, the server will connect to the address provided by the client. | |||
In both cases, the actual file or listing is then transferred over the data connection. | |||
Generally, establishing outgoing connections requires less configuration on the routers/firewalls involved than establishing incoming connections. In passive mode, the connection is outgoing on the client side and incoming on the server side and in active mode this is reversed. | |||
Note that the only differences are in establishing a connection. Once established, the connection can be used for uploads or downloads. | |||
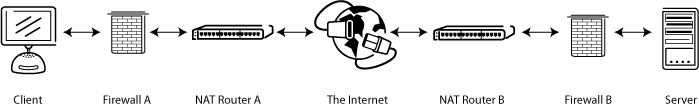
A common network setup might look like this: | |||
[ [Image : FTP1.png | center]] | [[Image:FTP1.png|center]] | ||
In passive mode, the router and firewall on the server side need to be configured to accept and forward incoming connections. On the client side, however, only outgoing connections need to be allowed (which will already be the case most of the time). | |||
Analogously, in active mode, the router and firewall on the client side need to be configured to accept and forward incoming connections. Only outgoing connections have to be allowed on the server side. | |||
Since in most cases one server provides a service for many users, it is much easier to configure the router and firewall on the server side once for passive mode than to configure the client's router/firewall for each individual client in active mode. Therefore, passive mode is recommended in most cases. | |||
==== NAT routers ==== | |||
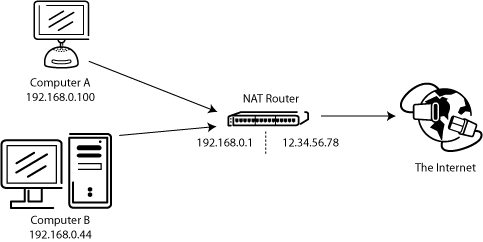
Most broadband users will have a NAT (Network Address Translation) router between their computer and the internet. This may be a standalone router device (perhaps a wireless router), or be built into a DSL or cable modem. In a NAT environment, all systems behind the NAT router form a ''Local Area Network (LAN)'', and each system in the LAN has a local IP address (recognizable as four small numbers separated by dots. See [http://en.wikipedia.org/wiki/Private_network Private addresses]). The NAT router itself has a local IP address as well. In addition, the NAT router also has an external IP address by which it is known to the Internet. | |||
An example system might look like this: | |||
[ [Image : FTP2.png | center]] | [[Image:FTP2.png|center]] | ||
The internal IP addresses are only valid inside the LAN, since they would make little sense to a remote system. Think about a server behind a NAT router. Imagine what might happen if a client requests passive mode, but the server doesn't know the external IP address of the NAT router. If the server sends its internal address to the client, two things could happen: | |||
* | * If the client is not behind a NAT, the client would abort since the address is invalid. | ||
* | * If the client is behind a NAT, the address given by the server might be the same as a system in the client's own LAN. | ||
Obviously, in both cases passive mode would be impossible. | |||
So if a server is behind a NAT router, it needs to know the external IP address of the router in passive mode. In this case, the server sends the router's external address to the client. The client then establishes a connection to the NAT router, which in turn routes the connection to the server. | |||
=== Firewalls === | |||
'' '' | ''Personal firewalls'' are installed on many systems to protect users from security vulnerabilities in the operating system or applications running on it. Over the internet, malware such as worms try to exploit these flaws to infect your system. Firewalls can help to prevent such an infection. However, firewalls and other security applications can sometimes interfere with non-malicious file transfers. | ||
Especially if using FTP, firewall users might occasionally see messages like this from their firewall: | |||
Trojan Netbus blocked on port 12345 used by FileZilla.exe | |||
In many cases, this is a false alarm. Any program can choose any port it wants for communication over the internet. FileZilla, then, might choose a port that is coincidentally also the default port of a trojan or some other malware being tracked by your firewall. FileZilla is clean of malware ''as long as it is downloaded from the official website''. | |||
=== | === Malicious routers, firewalls and data sabotage === | ||
Some routers and firewalls pretend to be smart. They analyze connections and, if they think they detect FTP, they silently change the data exchanged between client and server. If the user has not explicitly enabled this feature, this behavior is essentially data sabotage and can cause various problems. | |||
For an example, imagine a client behind a NAT router trying to connect to the server. Let's further assume that this client does not know it is behind a NAT and wants to use active mode. So it sends the PORT command with the user's local, un-routable IP address to the server: | |||
PORT 10,0,0,1,12,34 | |||
This command tells the server to connect to the address 10.0.0.1 on port 12*256+34 = 3106 | |||
The NAT router sees this and silently changes the command to include the external IP address. At the same time, the NAT router will also create a temporary port forwarding for the FTP session, possibly on a different port even: | |||
PORT 123,123,123,123,24,55 | |||
The above command tells the server to connect to the address 123.123.123.123 on port 24*256+55 = 6199 | |||
With this behavior, a NAT router allows an improperly configured client to use active mode. | |||
So why is this behavior bad? Essentially, it can cause a number of problems if it is enabled by default, without explicit user consent. The FTP connections in their most basic form appear to work, but as soon as there's some deviation from the basic case, everything will fail, leaving the user stumped: | |||
* | * The NAT router blindly assumes some connection uses FTP based on criteria like target ports or the initial server response: | ||
** | ** The used protocol is detected as FTP, yet there is no guarantee that this is true (a ''false positive''). Though unlikely, it is conceivable that a future revision of the FTP protocol might change the syntax of the PORT command. A NAT router modifying the PORT command would then silently change things it does not support and thus break the connection. | ||
** | ** The router's protocol detection can fail to recognize an FTP connection (a ''false negative''). Say the router only looks at the target port, and if it is 21, it detects it as FTP. As such, active mode connections with an improperly configured client to servers running on port 21 will work, but connections to other servers on non-standard ports will fail. | ||
* | * Obviously, a NAT router can no longer tamper with the connection as soon as an encrypted FTP session is used, again leaving the user clueless why it works for normal FTP but not for encrypted FTP. | ||
* | * Say a client behind a NAT router sends "PORT 10,0,0,1,12,34". How does the NAT router know the client is improperly configured? It is also possible that the client is properly configured, yet merely wants to initiate an FXP (server-to-server) transfer between the server it is connected to and another machine in the server's own local network. | ||
Therefore, having protocol specific features enabled in a NAT router by default can create significant problems. The solution to all this, then, is to know your router's settings, and to know the configuration abilities of a router before you set it up. A good NAT router should always be fully protocol-agnostic. The exception is if you as the user have explicitly enabled this feature, knowing all its consequences. | |||
While this section only discussed the combination of a NAT router on the client side with active mode, the same applies to a server behind a NAT router and the reply to the PASV command. | |||
== | == Setting up FileZilla Client == | ||
If you're running FileZilla 3, it's recommended you run the network configuration wizard. It will guide you through the necessary steps and can test your configuration after set-up. | |||
Obviously, if you want to connect to any server, you need to tell your firewall that FileZilla should be allowed to open connections to other servers. Most normal FTP servers use port 21, SFTP servers use port 22 and FTP over TLS (implicit mode) use port 990 by default. These ports are not mandatory, however, so it's best to allow outgoing connections to arbitrary remote ports. | |||
Since many servers on the internet are misconfigured and don't support both transfer modes, it's recommended that you configure both transfer modes on your end. | |||
=== === | === Passive mode === | ||
In passive mode, the client has no control over what port the server chooses for the data connection. Therefore, in order to use passive mode, you'll have to allow outgoing connections to all ports in your firewall. | |||
=== === | === Active mode === | ||
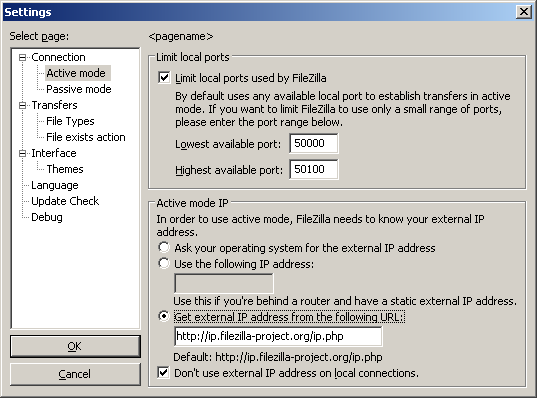
In active mode, the client opens a socket and waits for the server to establish the transfer connection. | |||
By default, FileZilla Client asks the operating system for the machine's IP address and for the number of a free port. This configuration can only work if you are connected to the internet directly without any NAT router, and if you have set your firewall to allow incoming connections on all ports greater than 1024. | |||
If you have a NAT router, you need to tell FileZilla your external IP address in order for active mode connections to work with servers outside your local network: | |||
* | * If you have a fixed external IP address, you can enter it in FileZilla's configuration dialog. | ||
* | * If you have a dynamic IP address, you can authorize FileZilla to obtain your external IP address from a special website. This will occur automatically each time FileZilla is started. No information will be submitted to the website (regardless of FileZilla version). | ||
If in doubt, use the second option. | |||
If you do not want to allow incoming connections on all ports, or if you have a NAT router, you need to tell FileZilla to use a specific range of ports for active mode connections. You will have to open these ports in your firewall. If you have a NAT router, you need to forward these ports to the local machine FileZilla is installed on. Depending on your router model, you can either forward a range of ports or you need to forward all ports individually. | |||
ports | Valid ports can be from 1 to 65535; however, ports less than 1024 are reserved for other protocols. It is best to choose ports greater than or equal to 50000 for active mode FTP. Due to the nature of [http://en.wikipedia.org/wiki/Transmission_Control_Protocol TCP] (the underlying transport protocol), a port cannot be reused immediately after each connection. Therefore, the range of ports should not be too small to prevent the failure of transfers of multiple small files. A range of 50 ports should be sufficient in most cases. | ||
<div align="center"> | <div align="center"> | ||
[ [Image : Settings_activemode.png | | [[Image:Settings_activemode.png|Screenshot of settings dialog of FileZilla 3 showing configuration page for active mode.]] | ||
</ | </div> | ||
== | == Setting up and testing FileZilla Server == | ||
{{Warning|The content of this section is '''outdated''' and '''needs to be adapted to apply''' to FileZilla Server version '''''1.x'''''}} | |||
Setting up the server is very similar to setting up the client, with the main difference being that the roles of active and passive mode are reversed. | |||
A common mistake, especially by users with NAT routers, is in testing the server. If you are within your local network, you can only test using the local IP address of the server. Using the external address from the inside will probably fail, and one of the following may happen: | |||
* It actually works (surprisingly - and it probably means something else is wrong ...) | |||
* The router blocks access to its own external address from the inside, due to identifying it as a possible attack | |||
* The router forwards the connection to your ISP, which then blocks it as a possible attack | |||
Even if the test works, there is no guarantee that an external user can really connect to your server and transfer files. The only reliable way to test your server is to try connecting from an external system, ''outside'' of your LAN. | |||
=== Active mode === | |||
Make sure FileZilla Server is allowed to establish outgoing connections to arbitrary ports, since the client controls which port to use. | |||
On the local end of the connection, FileZilla Server tries to use a port one less than that of the control connection (e.g. port 20 if server is listening on port 21). However, this is not always possible - so don't rely on it. | |||
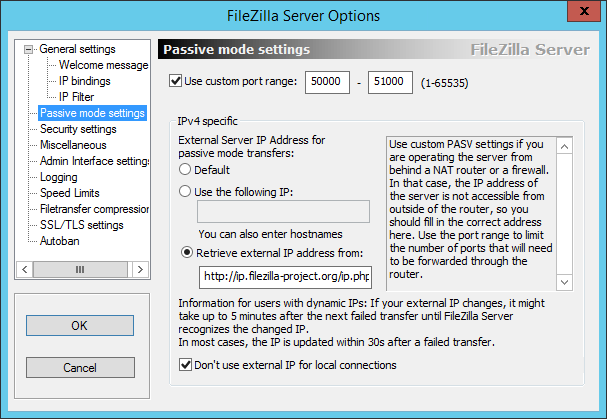
=== Passive mode === | |||
The server configuration is very similar to client configuration for active mode. In passive mode, the server opens a socket and waits for the client to connect to it. | |||
By default, FileZilla Server asks the operating system for the machine's IP address, and for a free port number. This configuration can only work if you are connected to the internet directly without any NAT router and if you have set your firewall to allow incoming connections on all ports greater than 1024. | |||
If you have a NAT router, you need to tell FileZilla Server your external IP address or passive mode connections will not work with clients outside your local network: | |||
* If you have a fixed external IP address, you can enter it in the configuration dialog of FileZilla Server. | |||
* If you have a dynamic IP address, you can let FileZilla Server obtain your external IP address from a special website automatically. Except your version of FileZilla Server, no information will be submitted to that website. | |||
If in doubt, use the second option. | |||
ports | If you do not want to allow incoming connections on all ports, or if you have a NAT router, you need to tell FileZilla Server to use a specific range of ports for passive mode connections. You will have to open these ports in your firewall. If you have a NAT router, you need to forward these ports to the local machine FileZilla Server is installed on. Depending on your router model, you can either forward a range of ports or you need to forward all ports individually. | ||
Valid ports can be from 1 to 65535, however ports less than 1024 are reserved for other protocols. It is best to choose ports >= 50000 for passive mode FTP. Due to the nature of [http://en.wikipedia.org/wiki/Transmission_Control_Protocol TCP] (the underlying transport protocol), a port cannot be reused immediately after each connection. Hence the range of ports should not be too small or transfers of multiple small files can fail. A range of 50 ports should be sufficient in most cases. | |||
<div align="center"> | <div align="center"> | ||
[ [Image : | [[Image:Settings_passivemode_FZServer.png||Screenshot of settings dialog of FileZilla Server showing configuration page for passive mode.]] | ||
</ | </div> | ||
== Troubleshooting == | |||
The following are a few troubleshooting suggestions: | |||
Unfortunately, many personal firewalls and consumer routers are flawed or in some cases, even actively sabotage FTP (e.g. [http://www.gbnetwork.co.uk/smcftpd/ SMC Barricade V1.2]). First of all, as with all software, you should keep everything updated. This includes the firewall software as well as the firmware version of your router. | |||
If that does not help, you might want to try to '''uninstall''' your firewall to see what happens. Simply disabling your firewall might not work, as some firewalls cannot be fully disabled. In particular, most firewalls install virtual device drivers which cannot be disabled other than by uninstalling them. Also check for hidden firewalls. Programs such as virus scanners often have firewall functionality as well. | |||
If possible, try to connect directly to the internet without a router by plugging your computer directly into your modem. If you have a combination modem/router device, try putting it into bridge mode to disable the routing part. | |||
If you are trying to setup a server and it works fine within your LAN but is not reachable from the outside, try changing the listening port. Some ISPs don't like their customers to host servers and they may block ports with numbers under 1024. | |||
Another issue may occur if you are hosting an FTP server on default port 21. There might be a firewall at the ISP side of your connection which can do odd things like changing the port for PASV commands. Try using another non-default port for your FTP server. | |||
If you encounter "cannot open data connection" on a random basis (i.e., the ftp client can connect to the ftp server without problem for many connections until it encounters this problem), one possible reason may be that your client PC anti-virus software is configured to block outgoing connections on certain ranges of ports. When your ftp connections are running in pasv mode, the client-side outgoing ports are selected randomly and some of those randomly selected ports may be blocked by the anti-virus software. To identify this problem, read your anti-virus log on the client. In general, any software that can block certain ranges of outgoing ports (such as PC firewalls) can cause similar FTP grief. | |||
=== Timeouts on large files === | |||
If you can transfer small files without any issues, but transfers of larger files end with a timeout, a broken router and/or firewall exists between the client and the server and is causing a problem. | |||
As mentioned above, FTP uses two TCP connections: a control connection to submit commands and receive replies, and a data connection for actual file transfers. It is the nature of FTP that during a transfer the control connection stays completely idle. | |||
The TCP specifications do not set a limit on the amount of time a connection can stay idle. Unless explicitly closed, a connection is assumed to remain alive indefinitely. However, many routers and firewalls automatically close idle connections after a certain period of time. Worse, they often don't notify the user, but just silently drop the connection. For FTP, this means that during a long transfer the control connection can get dropped because it is detected as idle, but neither client nor server are notified. So when all data has been transferred, the server assumes the control connection is alive and it sends the transfer confirmation reply. Likewise, the client thinks the control connection is alive and it waits for the reply from the server. But since the control connection got dropped without notification, the reply never arrives and eventually the connection will timeout. | |||
In an attempt to solve this problem, the TCP specifications include a way to send ''keep-alive packets'' on otherwise idle TCP connections, to tell all involved parties that the connection is still alive and needed. However, the TCP specifications also make it very clear that these keep-alive packets should not be sent more often than once every two hours. Therefore, with added tolerance for network latency, connections can stay idle for up to 2 hours and 4 minutes. | |||
However, many routers and firewalls drop connections that have been idle for less than 2 hours and 4 minutes. This violates the TCP specifications ([http://filezilla-project.org/specs/rfc5382.txt RFC 5382] makes this especially clear). In other words, all routers and firewalls that are dropping idle connections too early cannot be used for long FTP transfers. Unfortunately manufacturers of consumer-grade router and firewall vendors do not care about specifications ... all they care about is getting your money (and only deliver barely working lowest quality junk). | |||
To solve this problem, you need to uninstall affected firewalls and replace faulty routers with better-quality ones. | |||
== | == Setting up FileZilla Server with Windows Firewall == | ||
If you are having problems with setting up FileZilla Server to run behind Windows Firewall (specifically, it fails on "List" and the client receives a "Failed to receive directory listing" error), you must add the FileZilla Server application to Windows Firewall's Exceptions list. To do this, follow these steps: | |||
# | # Open Windows Firewall under Control Panel. | ||
# | # If using Vista, click "Change Settings" | ||
# | # Select the "Exceptions" tab. | ||
# | # Click "Add program..." | ||
# | # Do NOT select "FileZilla Server Interface" from the list, instead click on "Browse..." | ||
# | # Locate the directory you installed FileZilla Server to (normally "C:\Program Files\FileZilla Server\") | ||
# Double | # Double click or select "FileZilla server.exe" and press open (Once again, NOT "FileZilla Server Interface.exe") | ||
# | # Select "FileZilla server.exe" from the list and click "Ok" | ||
# | # Verify that "FileZilla server.exe" is added to the exceptions list and that it has a check mark in the box next to it | ||
# | # Press "Ok" to close the window | ||
# Open a command prompt with administrative rights and execute the following command: ''netsh advfirewall set global statefulftp disable'' | |||
Passive mode should now work. If you are still having problems connecting (from another computer or outside the network), check your router settings or try to add the port number in the [[Windows]] Firewall settings located in the Exceptions tab. | |||
See the Microsoft kb article 931130 about running FileZilla with the "Routing and Remote Access" or the "Application Layer Gateway" service enabled. | |||
http://support.microsoft.com/kb/931130 | http://support.microsoft.com/kb/931130 | ||
== Setting up FileZilla Server with Windows 8 Firewall == | |||
These are the instructions if your operating system is Windows 8 - the interface is slightly different from that described above in [[Network Configuration#Setting up FileZilla Server with Windows Firewall|Setting up FileZilla Server with Windows Firewall]]. | |||
Under Windows 8 you must allow the FileZilla Server application through Windows Firewall. To do this, follow these steps: | |||
# Move mouse to upper right corner and click the magnifying glass search icon, and type "firewall" (without the double quotes) in the Search box and then click the "Settings" text. Or, hold down the Windows logo key on the keyboard and press the I key, select the text "Control Panel" and press Enter, in the Search Control Panel area at top right type "firewall". In either case, now click the "Allow an app through Windows Firewall" that should appear. | |||
# Click "Change Settings" and a new button should appear titled "Allow another app..." | |||
# Click "Allow another app..." | |||
# A window titled "Add an app" should appear; do not do anything in this step. | |||
# Do NOT select "FileZilla Server Interface" from the list, instead click on "Browse..." | |||
# Locate the directory you installed FileZilla Server to (normally "C:\Program Files\FileZilla Server\") | |||
# Double click or select "FileZilla server.exe" and press open (Once again, NOT "FileZilla Server Interface.exe") | |||
# Your mouse pointer should now return to the "Add an app" window; scroll down the list and select "FileZilla server.exe" and click "Add". | |||
# Your mouse pointer should now return to the Windows Firewall Allowed apps window; verify that "FileZilla server.exe" is added to the allowed apps and features list and that it has a check mark in either the Private box or the Public box. Choose Private if you want the server accessible only from within your local network, and choose Public if you want the server accessible from outside your local network (this might include clients connected wirelessly to your network). | |||
# Press "Ok" to close the Windows Firewall window | |||
# Open a command prompt with administrative rights and execute the following command: ''netsh advfirewall set global statefulftp disable'' | |||
If you are still having problems see the advice at the end of section [[Network Configuration#Setting up FileZilla Server with Windows Firewall|Setting up FileZilla Server with Windows Firewall]] above or search Microsoft Knowledge base for Firewall related articles. | |||
Latest revision as of 00:33, 29 September 2023
Setting up network components for FTP is not trivial for use outside your LAN (Local Area Network). Since so many firewalls and routers exist, it is impractical to give detailed step-by-step instructions suitable for every user. It is important to understand the basics of the FTP protocol in order to configure FileZilla and the routers and/or firewalls involved. This documentation describes the history of the FTP and how some aspects of the protocol work. Reading it carefully will save you a lot of trouble setting up FTP.
Background
This section provides an overview of the historical and technical background of the FTP protocol. For detailed in-depth information see specifications.
Historical Background
In the fast living world of the internet, the File Transfer Protocol is not just old, it's ancient. Early drafts of the protocol go back as far as 1971, and the current specifications are from 1985. The protocol might even be older than you!
Back then, the Internet was mainly used by universities and research centers. The community was small, many users knew each other and all were collaborating together. The internet was a friendly, trusting place. Security was not much of a concern.
A lot has changed since then. The Internet is now ubiquitous, with millions of users communicating with each other in many different ways. It is also a more hostile place. The availability and openness has attracted malicious users who exploit design limitations, incomplete implementations, bugs, and the inexperience of other users.
Several attempts have been made to address these problems:
- NAT (Network Address Translation) routers. Many hosts and routers on the internet use the IPv4 protocol. The number of hosts connected to the internet has reached IPV4's design limit for the number of addresses (IPv6 is designed to relieve this). NAT routers allow multiple systems within a LAN to connect to the outside world with one external IP address.
- Personal firewalls try to protect personal computers from attacks by malicious users.
Unfortunately, both NAT and personal firewalls conflict with FTP more often than not. To make things worse, some are themselves flawed, causing additional problems regarding FTP.
Technical background
What distinguishes FTP from most other protocols is the use of secondary connections for file transfers. When you connect to an FTP server, you are actually making two connections. First, the so-called control connection is established, over which FTP commands and their replies are transferred. Then, in order to transfer a file or a directory listing, the client sends a particular command over the control connection to establish the data connection.
The data connection can be established two different ways, using active mode or passive mode.
In passive mode, which is recommended (see below), the client sends the PASV command to the server, and the server responds with an address. The client then issues a command to transfer a file or to get a directory listing, and establishes a secondary connection to the address returned by the server.
In active mode, the client opens a socket on the local machine and tells its address to the server using the PORT command. Once the client issues a command to transfer a file or listing, the server will connect to the address provided by the client.
In both cases, the actual file or listing is then transferred over the data connection.
Generally, establishing outgoing connections requires less configuration on the routers/firewalls involved than establishing incoming connections. In passive mode, the connection is outgoing on the client side and incoming on the server side and in active mode this is reversed. Note that the only differences are in establishing a connection. Once established, the connection can be used for uploads or downloads.
A common network setup might look like this:
In passive mode, the router and firewall on the server side need to be configured to accept and forward incoming connections. On the client side, however, only outgoing connections need to be allowed (which will already be the case most of the time).
Analogously, in active mode, the router and firewall on the client side need to be configured to accept and forward incoming connections. Only outgoing connections have to be allowed on the server side.
Since in most cases one server provides a service for many users, it is much easier to configure the router and firewall on the server side once for passive mode than to configure the client's router/firewall for each individual client in active mode. Therefore, passive mode is recommended in most cases.
NAT routers
Most broadband users will have a NAT (Network Address Translation) router between their computer and the internet. This may be a standalone router device (perhaps a wireless router), or be built into a DSL or cable modem. In a NAT environment, all systems behind the NAT router form a Local Area Network (LAN), and each system in the LAN has a local IP address (recognizable as four small numbers separated by dots. See Private addresses). The NAT router itself has a local IP address as well. In addition, the NAT router also has an external IP address by which it is known to the Internet.
An example system might look like this:
The internal IP addresses are only valid inside the LAN, since they would make little sense to a remote system. Think about a server behind a NAT router. Imagine what might happen if a client requests passive mode, but the server doesn't know the external IP address of the NAT router. If the server sends its internal address to the client, two things could happen:
- If the client is not behind a NAT, the client would abort since the address is invalid.
- If the client is behind a NAT, the address given by the server might be the same as a system in the client's own LAN.
Obviously, in both cases passive mode would be impossible.
So if a server is behind a NAT router, it needs to know the external IP address of the router in passive mode. In this case, the server sends the router's external address to the client. The client then establishes a connection to the NAT router, which in turn routes the connection to the server.
Firewalls
Personal firewalls are installed on many systems to protect users from security vulnerabilities in the operating system or applications running on it. Over the internet, malware such as worms try to exploit these flaws to infect your system. Firewalls can help to prevent such an infection. However, firewalls and other security applications can sometimes interfere with non-malicious file transfers.
Especially if using FTP, firewall users might occasionally see messages like this from their firewall:
Trojan Netbus blocked on port 12345 used by FileZilla.exe
In many cases, this is a false alarm. Any program can choose any port it wants for communication over the internet. FileZilla, then, might choose a port that is coincidentally also the default port of a trojan or some other malware being tracked by your firewall. FileZilla is clean of malware as long as it is downloaded from the official website.
Malicious routers, firewalls and data sabotage
Some routers and firewalls pretend to be smart. They analyze connections and, if they think they detect FTP, they silently change the data exchanged between client and server. If the user has not explicitly enabled this feature, this behavior is essentially data sabotage and can cause various problems.
For an example, imagine a client behind a NAT router trying to connect to the server. Let's further assume that this client does not know it is behind a NAT and wants to use active mode. So it sends the PORT command with the user's local, un-routable IP address to the server:
PORT 10,0,0,1,12,34
This command tells the server to connect to the address 10.0.0.1 on port 12*256+34 = 3106
The NAT router sees this and silently changes the command to include the external IP address. At the same time, the NAT router will also create a temporary port forwarding for the FTP session, possibly on a different port even:
PORT 123,123,123,123,24,55
The above command tells the server to connect to the address 123.123.123.123 on port 24*256+55 = 6199
With this behavior, a NAT router allows an improperly configured client to use active mode.
So why is this behavior bad? Essentially, it can cause a number of problems if it is enabled by default, without explicit user consent. The FTP connections in their most basic form appear to work, but as soon as there's some deviation from the basic case, everything will fail, leaving the user stumped:
- The NAT router blindly assumes some connection uses FTP based on criteria like target ports or the initial server response:
- The used protocol is detected as FTP, yet there is no guarantee that this is true (a false positive). Though unlikely, it is conceivable that a future revision of the FTP protocol might change the syntax of the PORT command. A NAT router modifying the PORT command would then silently change things it does not support and thus break the connection.
- The router's protocol detection can fail to recognize an FTP connection (a false negative). Say the router only looks at the target port, and if it is 21, it detects it as FTP. As such, active mode connections with an improperly configured client to servers running on port 21 will work, but connections to other servers on non-standard ports will fail.
- Obviously, a NAT router can no longer tamper with the connection as soon as an encrypted FTP session is used, again leaving the user clueless why it works for normal FTP but not for encrypted FTP.
- Say a client behind a NAT router sends "PORT 10,0,0,1,12,34". How does the NAT router know the client is improperly configured? It is also possible that the client is properly configured, yet merely wants to initiate an FXP (server-to-server) transfer between the server it is connected to and another machine in the server's own local network.
Therefore, having protocol specific features enabled in a NAT router by default can create significant problems. The solution to all this, then, is to know your router's settings, and to know the configuration abilities of a router before you set it up. A good NAT router should always be fully protocol-agnostic. The exception is if you as the user have explicitly enabled this feature, knowing all its consequences.
While this section only discussed the combination of a NAT router on the client side with active mode, the same applies to a server behind a NAT router and the reply to the PASV command.
Setting up FileZilla Client
If you're running FileZilla 3, it's recommended you run the network configuration wizard. It will guide you through the necessary steps and can test your configuration after set-up.
Obviously, if you want to connect to any server, you need to tell your firewall that FileZilla should be allowed to open connections to other servers. Most normal FTP servers use port 21, SFTP servers use port 22 and FTP over TLS (implicit mode) use port 990 by default. These ports are not mandatory, however, so it's best to allow outgoing connections to arbitrary remote ports.
Since many servers on the internet are misconfigured and don't support both transfer modes, it's recommended that you configure both transfer modes on your end.
Passive mode
In passive mode, the client has no control over what port the server chooses for the data connection. Therefore, in order to use passive mode, you'll have to allow outgoing connections to all ports in your firewall.
Active mode
In active mode, the client opens a socket and waits for the server to establish the transfer connection.
By default, FileZilla Client asks the operating system for the machine's IP address and for the number of a free port. This configuration can only work if you are connected to the internet directly without any NAT router, and if you have set your firewall to allow incoming connections on all ports greater than 1024.
If you have a NAT router, you need to tell FileZilla your external IP address in order for active mode connections to work with servers outside your local network:
- If you have a fixed external IP address, you can enter it in FileZilla's configuration dialog.
- If you have a dynamic IP address, you can authorize FileZilla to obtain your external IP address from a special website. This will occur automatically each time FileZilla is started. No information will be submitted to the website (regardless of FileZilla version).
If in doubt, use the second option.
If you do not want to allow incoming connections on all ports, or if you have a NAT router, you need to tell FileZilla to use a specific range of ports for active mode connections. You will have to open these ports in your firewall. If you have a NAT router, you need to forward these ports to the local machine FileZilla is installed on. Depending on your router model, you can either forward a range of ports or you need to forward all ports individually.
Valid ports can be from 1 to 65535; however, ports less than 1024 are reserved for other protocols. It is best to choose ports greater than or equal to 50000 for active mode FTP. Due to the nature of TCP (the underlying transport protocol), a port cannot be reused immediately after each connection. Therefore, the range of ports should not be too small to prevent the failure of transfers of multiple small files. A range of 50 ports should be sufficient in most cases.
Setting up and testing FileZilla Server
Warning: The content of this section is outdated and needs to be adapted to apply to FileZilla Server version 1.x
Setting up the server is very similar to setting up the client, with the main difference being that the roles of active and passive mode are reversed.
A common mistake, especially by users with NAT routers, is in testing the server. If you are within your local network, you can only test using the local IP address of the server. Using the external address from the inside will probably fail, and one of the following may happen:
- It actually works (surprisingly - and it probably means something else is wrong ...)
- The router blocks access to its own external address from the inside, due to identifying it as a possible attack
- The router forwards the connection to your ISP, which then blocks it as a possible attack
Even if the test works, there is no guarantee that an external user can really connect to your server and transfer files. The only reliable way to test your server is to try connecting from an external system, outside of your LAN.
Active mode
Make sure FileZilla Server is allowed to establish outgoing connections to arbitrary ports, since the client controls which port to use.
On the local end of the connection, FileZilla Server tries to use a port one less than that of the control connection (e.g. port 20 if server is listening on port 21). However, this is not always possible - so don't rely on it.
Passive mode
The server configuration is very similar to client configuration for active mode. In passive mode, the server opens a socket and waits for the client to connect to it.
By default, FileZilla Server asks the operating system for the machine's IP address, and for a free port number. This configuration can only work if you are connected to the internet directly without any NAT router and if you have set your firewall to allow incoming connections on all ports greater than 1024.
If you have a NAT router, you need to tell FileZilla Server your external IP address or passive mode connections will not work with clients outside your local network:
- If you have a fixed external IP address, you can enter it in the configuration dialog of FileZilla Server.
- If you have a dynamic IP address, you can let FileZilla Server obtain your external IP address from a special website automatically. Except your version of FileZilla Server, no information will be submitted to that website.
If in doubt, use the second option.
If you do not want to allow incoming connections on all ports, or if you have a NAT router, you need to tell FileZilla Server to use a specific range of ports for passive mode connections. You will have to open these ports in your firewall. If you have a NAT router, you need to forward these ports to the local machine FileZilla Server is installed on. Depending on your router model, you can either forward a range of ports or you need to forward all ports individually.
Valid ports can be from 1 to 65535, however ports less than 1024 are reserved for other protocols. It is best to choose ports >= 50000 for passive mode FTP. Due to the nature of TCP (the underlying transport protocol), a port cannot be reused immediately after each connection. Hence the range of ports should not be too small or transfers of multiple small files can fail. A range of 50 ports should be sufficient in most cases.
Troubleshooting
The following are a few troubleshooting suggestions:
Unfortunately, many personal firewalls and consumer routers are flawed or in some cases, even actively sabotage FTP (e.g. SMC Barricade V1.2). First of all, as with all software, you should keep everything updated. This includes the firewall software as well as the firmware version of your router.
If that does not help, you might want to try to uninstall your firewall to see what happens. Simply disabling your firewall might not work, as some firewalls cannot be fully disabled. In particular, most firewalls install virtual device drivers which cannot be disabled other than by uninstalling them. Also check for hidden firewalls. Programs such as virus scanners often have firewall functionality as well.
If possible, try to connect directly to the internet without a router by plugging your computer directly into your modem. If you have a combination modem/router device, try putting it into bridge mode to disable the routing part.
If you are trying to setup a server and it works fine within your LAN but is not reachable from the outside, try changing the listening port. Some ISPs don't like their customers to host servers and they may block ports with numbers under 1024.
Another issue may occur if you are hosting an FTP server on default port 21. There might be a firewall at the ISP side of your connection which can do odd things like changing the port for PASV commands. Try using another non-default port for your FTP server.
If you encounter "cannot open data connection" on a random basis (i.e., the ftp client can connect to the ftp server without problem for many connections until it encounters this problem), one possible reason may be that your client PC anti-virus software is configured to block outgoing connections on certain ranges of ports. When your ftp connections are running in pasv mode, the client-side outgoing ports are selected randomly and some of those randomly selected ports may be blocked by the anti-virus software. To identify this problem, read your anti-virus log on the client. In general, any software that can block certain ranges of outgoing ports (such as PC firewalls) can cause similar FTP grief.
Timeouts on large files
If you can transfer small files without any issues, but transfers of larger files end with a timeout, a broken router and/or firewall exists between the client and the server and is causing a problem.
As mentioned above, FTP uses two TCP connections: a control connection to submit commands and receive replies, and a data connection for actual file transfers. It is the nature of FTP that during a transfer the control connection stays completely idle.
The TCP specifications do not set a limit on the amount of time a connection can stay idle. Unless explicitly closed, a connection is assumed to remain alive indefinitely. However, many routers and firewalls automatically close idle connections after a certain period of time. Worse, they often don't notify the user, but just silently drop the connection. For FTP, this means that during a long transfer the control connection can get dropped because it is detected as idle, but neither client nor server are notified. So when all data has been transferred, the server assumes the control connection is alive and it sends the transfer confirmation reply. Likewise, the client thinks the control connection is alive and it waits for the reply from the server. But since the control connection got dropped without notification, the reply never arrives and eventually the connection will timeout.
In an attempt to solve this problem, the TCP specifications include a way to send keep-alive packets on otherwise idle TCP connections, to tell all involved parties that the connection is still alive and needed. However, the TCP specifications also make it very clear that these keep-alive packets should not be sent more often than once every two hours. Therefore, with added tolerance for network latency, connections can stay idle for up to 2 hours and 4 minutes.
However, many routers and firewalls drop connections that have been idle for less than 2 hours and 4 minutes. This violates the TCP specifications (RFC 5382 makes this especially clear). In other words, all routers and firewalls that are dropping idle connections too early cannot be used for long FTP transfers. Unfortunately manufacturers of consumer-grade router and firewall vendors do not care about specifications ... all they care about is getting your money (and only deliver barely working lowest quality junk).
To solve this problem, you need to uninstall affected firewalls and replace faulty routers with better-quality ones.
Setting up FileZilla Server with Windows Firewall
If you are having problems with setting up FileZilla Server to run behind Windows Firewall (specifically, it fails on "List" and the client receives a "Failed to receive directory listing" error), you must add the FileZilla Server application to Windows Firewall's Exceptions list. To do this, follow these steps:
- Open Windows Firewall under Control Panel.
- If using Vista, click "Change Settings"
- Select the "Exceptions" tab.
- Click "Add program..."
- Do NOT select "FileZilla Server Interface" from the list, instead click on "Browse..."
- Locate the directory you installed FileZilla Server to (normally "C:\Program Files\FileZilla Server\")
- Double click or select "FileZilla server.exe" and press open (Once again, NOT "FileZilla Server Interface.exe")
- Select "FileZilla server.exe" from the list and click "Ok"
- Verify that "FileZilla server.exe" is added to the exceptions list and that it has a check mark in the box next to it
- Press "Ok" to close the window
- Open a command prompt with administrative rights and execute the following command: netsh advfirewall set global statefulftp disable
Passive mode should now work. If you are still having problems connecting (from another computer or outside the network), check your router settings or try to add the port number in the Windows Firewall settings located in the Exceptions tab.
See the Microsoft kb article 931130 about running FileZilla with the "Routing and Remote Access" or the "Application Layer Gateway" service enabled. http://support.microsoft.com/kb/931130
Setting up FileZilla Server with Windows 8 Firewall
These are the instructions if your operating system is Windows 8 - the interface is slightly different from that described above in Setting up FileZilla Server with Windows Firewall.
Under Windows 8 you must allow the FileZilla Server application through Windows Firewall. To do this, follow these steps:
- Move mouse to upper right corner and click the magnifying glass search icon, and type "firewall" (without the double quotes) in the Search box and then click the "Settings" text. Or, hold down the Windows logo key on the keyboard and press the I key, select the text "Control Panel" and press Enter, in the Search Control Panel area at top right type "firewall". In either case, now click the "Allow an app through Windows Firewall" that should appear.
- Click "Change Settings" and a new button should appear titled "Allow another app..."
- Click "Allow another app..."
- A window titled "Add an app" should appear; do not do anything in this step.
- Do NOT select "FileZilla Server Interface" from the list, instead click on "Browse..."
- Locate the directory you installed FileZilla Server to (normally "C:\Program Files\FileZilla Server\")
- Double click or select "FileZilla server.exe" and press open (Once again, NOT "FileZilla Server Interface.exe")
- Your mouse pointer should now return to the "Add an app" window; scroll down the list and select "FileZilla server.exe" and click "Add".
- Your mouse pointer should now return to the Windows Firewall Allowed apps window; verify that "FileZilla server.exe" is added to the allowed apps and features list and that it has a check mark in either the Private box or the Public box. Choose Private if you want the server accessible only from within your local network, and choose Public if you want the server accessible from outside your local network (this might include clients connected wirelessly to your network).
- Press "Ok" to close the Windows Firewall window
- Open a command prompt with administrative rights and execute the following command: netsh advfirewall set global statefulftp disable
If you are still having problems see the advice at the end of section Setting up FileZilla Server with Windows Firewall above or search Microsoft Knowledge base for Firewall related articles.