Network Configuration
Setting up network components for FTP is not trivial for use outside your LAN (Local Area Network). Since so many firewalls and routers exist, it is impractical to give detailed step-by-step instructions suitable for every user. To configure FileZilla and the routers and/or firewalls involved, it is important to understand the basics of the FTP protocol. This documentation describes the history of the FTP protocol and how some aspects of the protocol work. Read it carefully, it will save you a lot of trouble setting up FTP.
Baggrund
En oversigt over de historiske og tekniske baggrund af FTP-protokollen. For detaljeret dybdegående information se specifikationer.
Historisk Baggrund
Jeg DET hurtigt Levende Verden AF internettet, ER File Transfer Protocol ikke bare Gamle, DET ER Gamle. Tidlige udkast AF protokollen Går sa Langt Tilbage SOM 1971, MED de nuværende Specifikationer, der FRA 1985. Protokollen Maske endda be Ældre ende grave!
Dengang var Internettet primært anvendes AF universiteter OG forskningscentre. Fællesskabet var beskeden, skab brugere kendte hinanden OG Allé var samarbejder sammen. Internettet var da venlig, tillidsfuld Sted. Sikkerhed var ikke en bekymring.
Siden da Administrator massevis ændret. Internettet ER Nu allestedsnærværende, MED millioner AF brugere på kommunikere MED hinanden in skab forskellige Mader. Internettet ER Nu da fjendtlig Sted. Tilgængeligheden OG åbenhed Administrator tiltrukket hackere, der udnytter design begrænsninger, ufuldstændige implementeringer, benytter normalt OG manglende erfaring Andre brugere. Et velkendt software Selskab i Redmond, WA sikkert spillet en Rolle.
Fri mærkning forsøg Administrator været Gjört i miste disse problemer:
- [Http: / / en.wikipedia.org / wiki / Network_address_translation NAT] (Network Address Translation) routere. Skab AF de værter OG routere in internettet Bruge IPv4 TAGER. Antallet AF værter tilsluttet Til internettet is ved på Na IPV4 design grænse for antallet AF Adresser (IPv6 is designet Til at lindre This page). NAT-routere tillader Fri mærkning Systemer inden for en LAN Til at oprette forbindelse Til omverdenen MED EN ekstern IP Adresse.
- [Http: / / en.wikipedia.org / wiki / Personal_firewall Personlige firewalls] forsøger at beskytte personlige Computere mod Angreb FRA hackere.
Desværre bød NAT OG personlige firewalls konflikt MED FTP oftere ende ikke. For at gore tingene værre, SIG nogle AF DEM Administrator endda Mangler SELV, skaber yderligere problemer MED FTP.
Teknisk Baggrund
DET, der adskiller FTP FRA de fleste Andre protokoller is brugen AF sekundære forbindelser for filoverførsler. Hvis du opretter forbindelse Til en FTP-server, SKAL du oprette de såkaldtekontrol forbindelse, over hvilken FTP kommandoer OG deres svar ER overført. For at overføre en fil Eller da Mappe Free, forbindelse afsenderen klienten en Kommando over kontrollen på etableredataforbindelse.
This dataforbindelse KAN etableres in til forskellige Mader, også kaldet Aktiv tilstand OG passiv tilstand.
Jeg passiv tilstand, SOM ER den anbefalede tilstand, afsender kunden PASV Kommando Til Serveren, OG Serveren Svarer MED en Adresse. Klienten derefter udsteder en Kommando Til at overføre en fil Eller på fa en Mappe Free OG etablerer en Sekundær tilknytning Til den Adresse, der returneres AF Serveren.
Jeg Aktiv tilstand, Åbner kunden et Stik in den Lokale Maskine, OG fortæller synd Adresse Til Serveren ved hjælp AF PORT kommandoen. Nar kunden afgiver en Kommando Til at overføre en fil Eller Free, VII, Serveren skal forbinde Til den Adresse, SOM kunden.
Jeg begge tilfælde den faktiske fil Eller Free overføres derefter via dataforbindelse.
Generelt kræver oprettelse udgående forbindelser mindre Konfiguration in router / firewalls involveret udgangen oprettelse indgående forbindelser. Jeg passiv tilstand, ER forbindelsen udgående in klientsiden OG indgående in Serveren side. Jeg Aktiv tilstand is hund rollerne Vendt: Den dataforbindelse is indgående in klientsiden OG udgående in Serveren side. Bemærk venligst at dette Kun gor en ForskEL for tilslutning etablering: Nar dataforbindelsen bliver Oprettet DET KAN Bruges Til Docenter op-Eller downloads.
En fælles Netværk setup kunne se Sadan UD:
SA i passiv tilstand, router OG firewall in Serveren side Skal konfigureres Til at acceptere OG videresende indgående forbindelser. In klientsiden Administrator hund Kun udgående forbindelser på fa lov, SOM allerede VII, be tilfældet DET meste AF tiden.
Tilsvarende i Aktiv tilstand, router OG firewall in klientsiden Skal konfigureres Til at acceptere OG videresende indgående forbindelser. Tilsyneladende in Serveren side, Kun udgående forbindelser Skal be tilladt.
Da Regel en server leverer en tjeneste for sukkerærter brugere, ER DET Langt nemmere ved bare Konfigureret routeren OG firewall in Serveren side en bande for passiv tilstand, slutter kl Konfigureret kundens router / firewall til hver Enkelt Kunde i Aktiv tilstand. Derfor ER passiv tilstand anbefales.
NAT routere
For de fleste bredbåndsbrugere, OG VII, der be en NAT (Network Address Translation) router mellem deres computer Internettet. This NAT router KAN be en standalone router Enhed (Maske en Trådløs router), Eller DET kunne be indbygget i en DSL Eller kabelmodem. I DA NAT Miljø, omhu Systemer taske NAT router form enLocal Area Network (LAN)OG hvert system i LAN Advocate en Lokal IP-Adresse (genkendes SOM brand Små tal adskilt AF punktummer). NAT router SELV Advocate en Lokal IP Adresse. Hertil Kommer på også NAT routeren Advocate en ekstern IP Adresse, hvorunder DET ER kendt AF Internettet. De Interne IP Adresser is Kun gyldige inden for internet, for en ekstern system, de Ville ikke give Nøgen mening. Eksempel:
Antager en server is pose en NAT router. Forestil dig, Finde sker der, hvis en Kunde anmoder passiv tilstand, mænd Serveren ikke kender eksterne IP Adresse NAT router. SA Serveren afsender sinus Interne Adresse Til klienten. I SA Fald til tinget KAN SKE:
- Hvis klient is ikke taske da NAT, VII, kunden afbryde da-Adresse ER ugyldig.
- Hvis klient is taske da NAT, anførte Adresse AF Serveren KAN be de samme SOM et system i kundens eget LAN.
DET ER klart, i begge tilfælde passiv tilstand Ville be umuligt.
SA hvis en server is pose en NAT router, ER DET nødvendigt på Kende den eksterne IP Adresse in routeren i passiv tilstand. I SA Fald afsender Serveren routerens eksterne Adresse Til klienten. Klienten derefter etablerer en forbindelse Til NAT router, SOM Igen Ruter forbindelsen Til Serveren.
Firewalls
Formålet med enPersonal Firewaller at beskytte brugeren fra sikkerhedshuller i operativsystemet eller applikationer, der kører på det. Over internettet. Malware som f.eks orm forsøger at udnytte fejlene til at inficere dit system Firewalls kan medvirke til at forebygge en sådan infektion.
Især hvis du bruger FTP, kan firewall brugere undertiden se indlæg som dette fra deres firewall: Trojan Netbus blokeret på porten 12345. bruges af FileZilla.exe
I næsten alle tilfælde er det enfalsk alarm. Enhver program kan vælge en havn det vil have for kommunikation over internettet. Så det kan ske, at FileZilla sker for at vælge en port, der i øvrigt standard havn i en trojan eller anden malware. Så længe du henter FileZilla fra den officielle hjemmeside, det er ren eventuelle malware.
Ondskabsfuld routere, firewalls og data sabotage
Nogle routere og firewalls foregive at være smart. De analysere forbindelser, og hvis de tror det er FTP, de tavse ændre data, der udveksles mellem klient og server. Hvis brugeren ikke har udtrykkeligt slået denne funktion, denne adfærd er intet andet end data sabotage og kan forårsage forskellige problemer.
For at illustrere med et eksempel, antage, at der er en klient bag en NAT router forsøger at oprette forbindelse til serveren. Lad os yderligere antage, at denne kunde ikke vide det er bag en NAT og ønsker at bruge aktiv tilstand. Så det sender PORT kommando med sit lokale, unroutable IP-adresse til serveren:
PORT 10,0,0,1,12,34
Ovenstående kommando fortæller serveren at forbinde til den adresse 10.0.0.1 på port 12 * 256 34 = 3.106
NAT router ser dette og lydløst ændrer kommandoen til at omfatte den eksterne IP-adresse. Samtidig vil NAT router også oprette en midlertidig port forwarding for FTP-session, eventuelt på en anden port selv:
PORT 123,123,123,123,24,55
Nu ovenstående kommando fortæller serveren at forbinde til den adresse, 123.123.123.123 på port 24 * 256 55 = 6.199
Med denne adfærd, kan en NAT router en forkert konfigurerede klient til at bruge aktiv tilstand.
Men hvorfor er det dårligt? Hvis denne funktion er aktiveret som standard, uden udtrykkelig brugerens samtykke, det forårsager mange problemer. FTP-forbindelser i sin mest basale form synes at arbejde, men så snart der er nogle afvigelser fra de grundlæggende tilfældet, vil alt mislykkes, forlader brugeren helt forvirrede:
- Den NAT-router blindt antager nogle forbindelse bruger FTP baseret på kriterier som mål havne eller den oprindelige server svar:
- Der er ingen garanti for, at den anvendte protokol er virkelig FTP, men den er opdaget som sådan (også kaldetfalsk positive). Selvom usandsynligt, er det tænkeligt, at der i en kommende revision af FTP-protokollen, kan syntaksen for PORT kommando forandring. En NAT router ændre PORT kommando vil tavst ændre ting, det ikke støtte og dermed bryde forbindelsen.
- Routeren's protokol opdagelse kan undlade at anerkende en FTP-forbindelse (enfalsk negative). Lad os antage, at routeren kun ser på målet havn, og hvis det er 21, den opdager det som FTP. Som sådan aktiv tilstand forbindelser med en forkert konfigurerede klient til servere, der kører på port 21 vil arbejde, men forbindelser til andre servere på ikke-standard havnene vil mislykkes.
- Selvfølgelig kan en NAT router ikke længere manipulere med forbindelsen, så snart en krypteret FTP session bruges igen forlader brugeren clueless hvorfor det virker for normal FTP men ikke for krypteret FTP.
- Antag en klient bag en NAT router sender "PORT 10,0,0,1,12,34". Hvordan NAT router kender kunden er forkert konfigureret? Det er også muligt, at kunden er konfigureret korrekt, men blot ønsker at indlede en FXP (server til server) overførsel mellem serveren, den er tilsluttet og en anden maskine i serverens eget lokale netværk.
Som du kan se, der protokol særlige træk aktiveret i en NAT router som standard er en dårlig ting. En god NAT router bør altid være fuldt protokol-agnostisk. Undtagelsen er, hvis du som bruger udtrykkeligt har slået denne funktion til, vel vidende alle dens konsekvenser.
Selv om dette afsnit er kun drøftet kombinationen af en NAT router på klientsiden med aktiv tilstand, gælder det samme til en server bag en NAT router og svaret på PASV kommandoen.
Setting up FileZilla Client
In case you're running FileZilla 3, it's recommended you run the network configuration wizard. It will guide you through the necessary steps and can test your configuration in the end.
Obviously, if you want to connect to any server, you need to tell your firewall that FileZilla should be allowed to open connections to other servers. Most normal FTP servers use port 21, SFTP servers use port 22 and FTP over SSL/TLS (implicit mode) use port 990 by default. These ports are not mandatory though, so it's best to allow outgoing connections to arbitrary remote ports.
Since there are many servers on the internet that are misconfigured and don't support both transfer modes, it's recommended that you configure both transfer modes on your end.
Passive mode
The client has no control over what port the server chooses for the data connection in passive mode, so in order to use passive mode, you'll have to allow outgoing connections to all ports in your firewall.
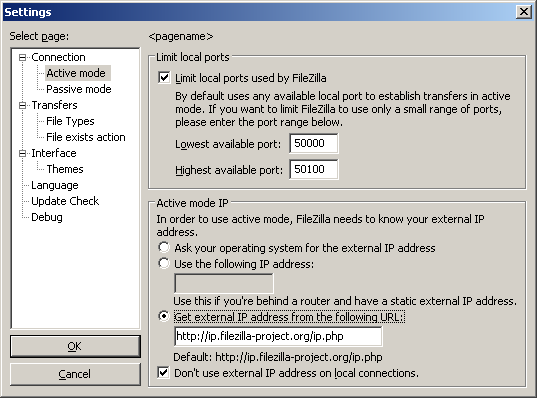
Active mode
In active mode, the client opens a socket and waits for the server to establish the transfer connection.
By default, FileZilla Client asks the operating system for the machine's IP address and for a free port number. This configuration can only work if you are connected to the internet directly without any NAT router and if you have set your firewall to allow incoming connections on all ports greater than 1024.
If you have a NAT router, you need to tell FileZilla your external IP address or active mode connections will not work with servers outside your local network:
- If you have a fixed external IP address, you can enter it in the configuration dialog of FileZilla.
- If you have a dynamic IP address, you can let FileZilla obtain your external IP address from a special website automatically each time you start FileZilla. No matter what version of FileZilla you have, no information will be submitted to that website.
If in doubt, use the second option.
If you do not want to allow incoming connections on all ports, or if you have a NAT router, you need to tell FileZilla to use a specific range of ports for active mode connections. You will have to open these ports in your firewall. If you have a NAT router, you need to forward these ports to the local machine FileZilla is installed on. Depending on your router model, you can either forward a range of ports or you need to forward all ports individually.
Valid ports can be from 1 to 65535, however ports less than 1024 are reserved for other protocols. It is best to choose ports greater than or equal to 50000 for active mode FTP. Due to the nature of TCP (the underlying transport protocol), a port cannot be reused immediately after each connection. Hence the range of ports should not be too small or transfers of multiple small files can fail. A range of 50 ports should be sufficient in most cases.
Setting up FileZilla Server
Setting up the server is very similar to setting up the client, the main difference is that the roles of active and passive mode are reversed.
One common mistake done especially from users with NAT routers is the way they test the server. If you are within your local network, you can only test using the local IP address of the server. Using the external address from the inside will probably fail. Basically one of the following could happen if you try to connect using the external address from the inside:
- It surprisingly works
- Router blocks access to its own external address from the inside as possible attack
- Router forwards connection to your ISP which then blocks it as possible attack
Even if that works, there is no guarantee an external user can really connect to your server and transfer files. The only reliable way is to connect to your server from an external system outside of your LAN.
Active mode
Just make sure FileZilla Server is allowed to establish outgoing connections to arbitrary ports, since the client controls which port to use.
For the local end of the connection, FileZilla Server tries to use a port one less than that of the control connection (e.g. port 20 if server is listening on port 21). However this is not always possible, so don't rely on it.
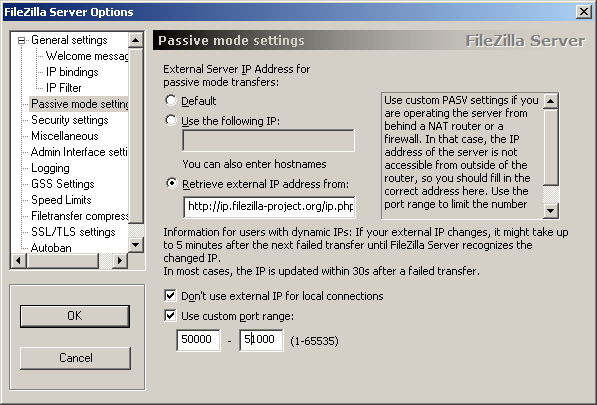
Passive mode
Server configuration is very similar to client configuration for active mode.
In passive mode, the server opens a socket and waits for the client to connect to it.
By default, FileZilla Server asks the operating system for the machine's IP address and for a free port number. This configuration can only work if you are connected to the internet directly without any NAT router and if you have set your firewall to allow incoming connections on all ports greater than 1024.
If you have a NAT router, you need to tell FileZilla Server your external IP address or passive mode connections will not work with clients outside your local network:
- If you have a fixed external IP address, you can enter it in the configuration dialog of FileZilla Server.
- If you have a dynamic IP address, you can let FileZilla Server obtain your external IP address from a special website automatically. Except your version of FileZilla Server, no information will be submitted to that website.
If in doubt, use the second option.
If you do not want to allow incoming connections on all ports, or if you have a NAT router, you need to tell FileZilla Server to use a specific range of ports for passive mode connections. You will have to open these ports in your firewall. If you have a NAT router, you need to forward these ports to the local machine FileZilla Server is installed on. Depending on your router model, you can either forward a range of ports or you need to forward all ports individually.
Valid ports can be from 1 to 65535, however ports less than 1024 are reserved for other protocols. It is best to choose ports >= 50000 for passive mode FTP. Due to the nature of TCP (the underlying transport protocol), a port cannot be reused immediately after each connection. Hence the range of ports should not be too small or transfers of multiple small files can fail. A range of 50 ports should be sufficient in most cases.
Troubleshooting
Unfortunately, many personal firewalls and consumer routers are flawed or in some cases, are even actively sabotaging FTP (e.g. SMC Barricade V1.2).
First of all, you should keep everything up-to-date. This includes the firewall software as well as the firmware version in your router.
If that does not help, you might want to try to uninstall your firewall to see what happens. Simply disabling your firewall might not work, as some firewalls cannot be fully disabled.
If possible, try to connect directly to the internet without a router.
If you are trying to setup a server and it works fine within your LAN but is not reachable from the outside, try changing the listening port. Some ISPs don't like its customers to host servers and block ports < 1024.
Another problem might be if you are hosting an FTP server on default port 21. There might be a firewall at the ISP side of your connection which can do odd things like changing the port for PASV commands. Try using another non-default port for your FTP server.
If you encounter "cannot open data connection" on a random basis, i.e. the ftp client can connect to the ftp server without problem for many connections until it encounters this problem, one possible reason may be your client PC anti-virus scanner being configured to block outgoing connections on certain ranges of ports. When your ftp connections are running on pasv mode, the client side outgoing ports are selected randomly and when it hits those prohibited ports, you will encounter your problem. To identify this problem, read your anti-virus log on that client. In general, any software e.g. PC firewall, etc that can block certain range of outgoing ports can cause similar ftp grief.
Timeouts on large files
If you can transfer small files just fine, but transfers of larger files end with a timeout, then there is a broken router and/or firewall between the client and the server that is causing this problem.
As mentioned above, FTP uses two TCP connections: One control connection to submit commands and to receive replies as well as one data connection for the actual file transfers. It is the nature of FTP that during a transfer the control connection stays completely idle.
The TCP specifications do not set a limit on the amount of time a connection can stay idle. Unless explicitly closed a connection is assumed to remain alive indefinitely. Many routers and firewalls however automatically close idle connections after a while. Worse, they most of the time don't even notify the endpoints of this, instead they just silently drop the connection. So for FTP this means that during a long transfer the control connection can get dropped, but neither client nor server get to know about it. So when all data has been transferred, the server still thinks the control connection is alive and sends the transfer confirmation reply over the control connection. Likewise, the client as well thinks the control connection is alive and waits for the reply from the server. But since the control connection got silently dropped, this reply never arrives, eventually causing a timeout.
In an attempt to solve this problem, the TCP specifications include a way to send keep-alive packets on otherwise idle TCP connections, to tell all involved parties that the connection is still alive and needed. However, the TCP specifications also make it very clear that these keep-alive packets should not be sent more often than once every two hours. Thus, with added tolerance for network latency, connections can stay idle for up to 2 hours and 4 minutes.
The problem is that many routers and firewalls drop connections that have been idle for less than 2 hours and 4 minutes. Such behavior is violating the TCP specifications, RFC 5382 makes this very clear. In other words, all routers and firewalls that are dropping idle connections too early are broken, they just cannot be used for long FTP transfers. Unfortunately manufacturers of consumer-grade router and firewall vendors do not care about specifications, all they care about is getting your money and thus only deliver barely working lowest quality junk.
To solve this problem you need to uninstall any affected firewall and replace any faulty router with a quality one.
Setting up FileZilla Server with Windows Firewall
If you are having problems with setting up FileZilla Server to run behind Windows Firewall (specifically, it fails on "List" and the client receives a "Failed to receive directory listing" error), you must add the FileZilla Server application to Windows Firewall's Exceptions list. To do this, follow these steps:
- Open Windows Firewall under Control Panel.
- If using Vista, click "Change Settings"
- Select the "Exceptions" tab.
- Click "Add program..."
- Do NOT select "FileZilla Server Interface" from the list, instead click on "Browse..."
- Locate the directory you installed FileZilla Server to (normally "C:\Program Files\FileZilla Server\")
- Double click or select "FileZilla server.exe" and press open (Once again, NOT "FileZilla Server Interface.exe")
- Select "FileZilla server.exe" from the list and click "Ok"
- Verify that "FileZilla server.exe" is added to the exceptions list and that it has a check mark in the box next to it
- Press "Ok" to close the window
Passive mode should now work. If you are still having problems connecting (from another computer or outside the network) check your router settings or try to add the port number in the Windows Firewall settings located in the Exceptions tab.
See the Microsoft kb article 931130 about running FileZilla with the "Routing and Remote Access" or the "Application Layer Gateway" service enabled. http://support.microsoft.com/kb/931130